Setup an Auth0 Identity Provider
Prerequisites
Sign up with Auth0 or login if you already have an account.
Configure Auth0
Skip the Auth0 onboarding tutorials and go straight to your dashboard.
Create a new application
1. Name it something meaningful
We will be connecting to a 'regular web application'.

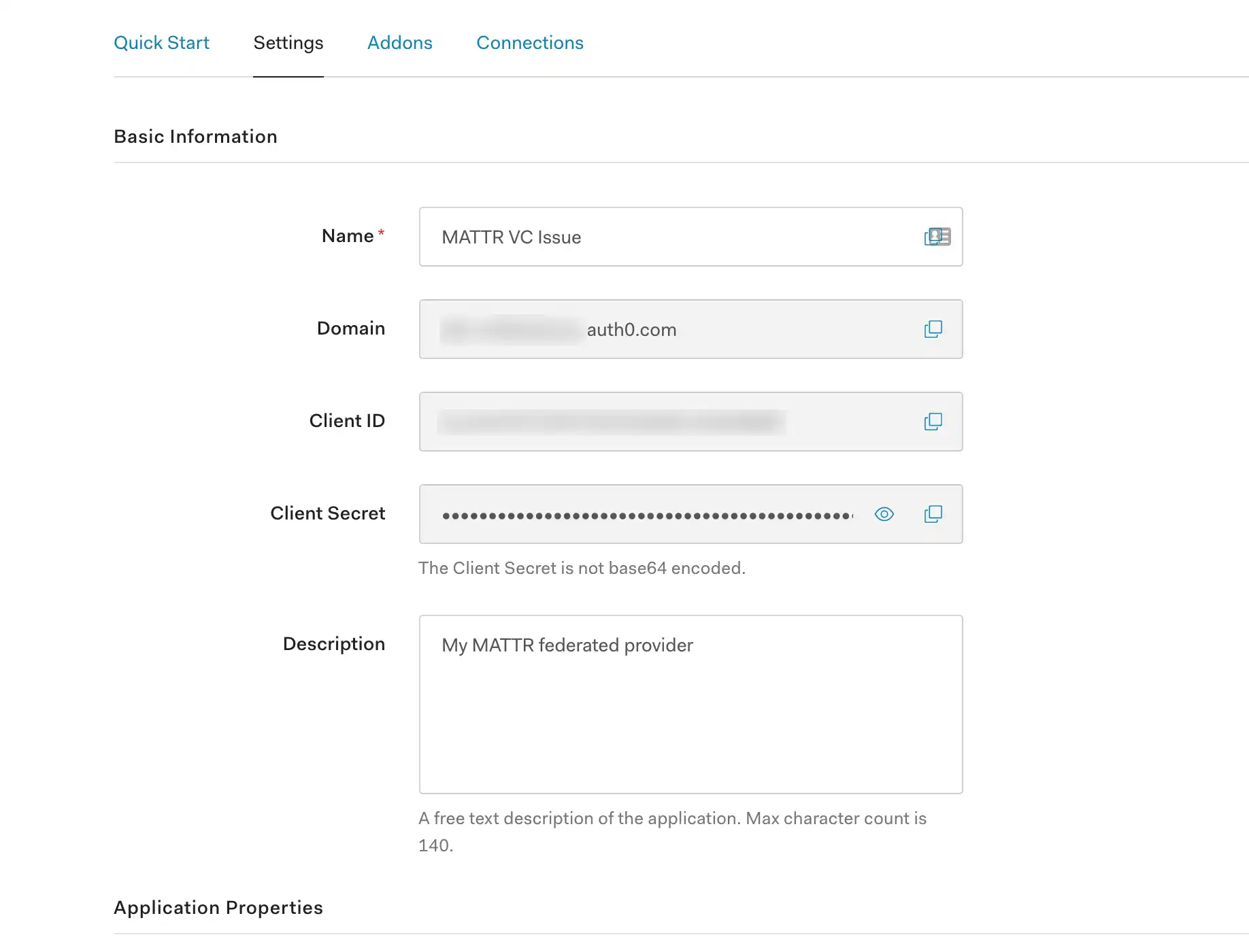
2. Skip the 'Quick Start' and navigate to the 'Settings' tab.
Make note of the:
- Domain
- Client ID
- Client Secret
Edit these fields:
Add a simple description
In the 'Allowed Callback URLs' section add in
https://example.com/callback. This will be used later during the manual testing.
All other fields can be left at their default values.
3. Make sure your OpenID Configuration is discoverable by browsing to https://<your-auth0-domain>.auth0.com/.well-known/openid-configuration and checking that the following values exist (other options may sit alongside):
1{
2 "authorization_endpoint": "https://your-auth-endpoint/authorize",
3 "token_endpoint": "https://your-token-endpoint/token",
4 "jwks_uri": "https://your-jwks-endpoint/jwks.json",
5 "response_types_supported": [
6 "code"
7 ],
8 "grant_types_supported": [
9 "authorization_code"
10 ],
11}
Setup a connection and add users
This is where Auth0 is used to store and hold user information, including PII. Before you add details about users, make sure you understand Auth0's policies around storing this information.
4. Navigate to the 'Connections' tab:
Leave Database and Username-Password-Authentication Enabled
Disable the Social login
5. Click Users under User Management on the left-hand side navigation panel.
Select Create User.
Provide an email address that is different to the Admin account used to sign up with Auth0.
Add a password.
Leave Connection as 'Username-Password-Authentication'.
Optional: you may want to update the default `Name` field from just being the email address to something more meaningful.
⚠️ Warning
Auth0 restricts the size of the ID Token to 100Kb. Ensure that the data you inject into your token is below this limit or credential issuance will fail. Also, it is not recommended to use authentication provider as a source of claims for the issuance of credentials, bur rather configure a claims source instead.
What's next?
You can now continue to configure your identity provider in MATTR VII.